Introduction
In the digital world, keeping our cloud and container systems safe is a big deal, the significance of regular security checkups cannot be overstated. We all recognize the critical importance of safeguarding our cloud environments, yet the manual scrutiny of resources can be a daunting and time-consuming task. In this exploration, we will unravel the power of cutting-edge open-source tools that empower us to conduct thorough security scans for both AWS and Kubernetes environments. That’s where special tools come in, Meet Kubebench for Kubernetes and Prowler for AWS – our trusty helpers open-source tools.
Meet Kubebench
Kubebench is like a guardian for Kubernetes. It’s a Go application that checks if Kubernetes is set up securely. It does this by running tests outlined in the CIS Kubernetes Benchmark. The cool thing is, you can easily update it because the tests are configured with simple YAML files.
Here’s a quick look at what Kubebench has uncovered in the security exploration:
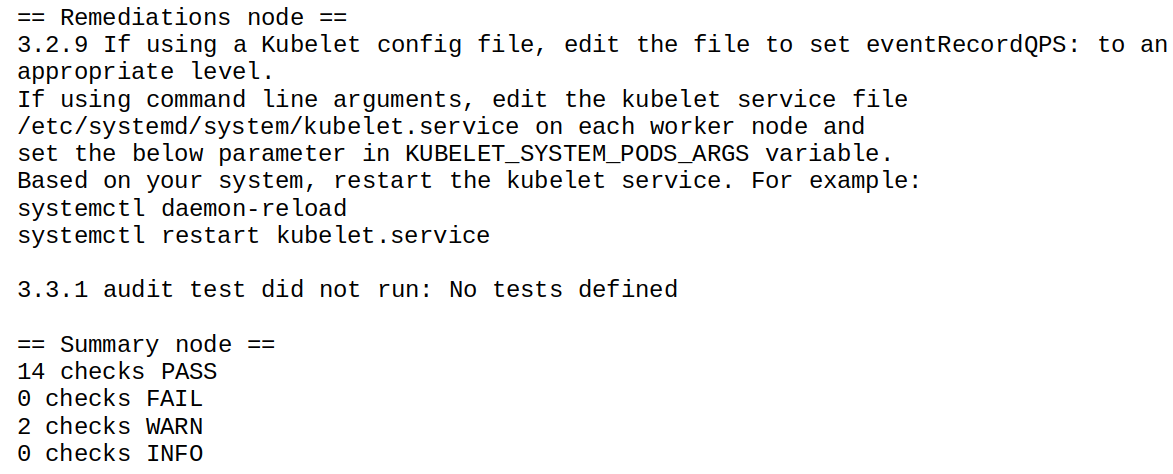
It’s like a handy assistant that makes sure your Kubernetes setup is secure. It does this by running tests based on a standard called the CIS Kubernetes Benchmark. What’s cool is you can easily update it using simple files.
Prowler - Security Hero for AWS
On the AWS side, we have Prowler, a versatile security superhero that extends its watchful eye to AWS, Azure, and GCP. Prowler doesn’t just stand by; it actively performs crucial tasks to keep our cloud environments secure.
Installation and Prerequisites
Before Prowler can start its superhero duties, we need to set it up. Here’s a simple guide:
Step 1: Install Prowler
Make sure you have Python > ~ 3.9 installed, and then install Prowler using pip:
$ ‘pip install prowler’
Step 2: Configure AWS CLI
Prowler needs to connect to your cloud, so configure your AWS CLI with the necessary credentials. Make sure the credentials are associated with a user or role that has the right permissions. To be sure, add these AWS managed policies to the user or role:
arn:aws:iam::aws:policy/SecurityAudit
arn:aws:iam::aws:policy/job-function/ViewOnlyAccessStep 3: Run Prowler
Now, you’re ready to run Prowler. Use the following command:
$ ‘prowler <provider> -M csv json json-asff html’
Replace <provider> with your cloud provider. This command performs a comprehensive security scan, and you’ll get a detailed output in various formats.
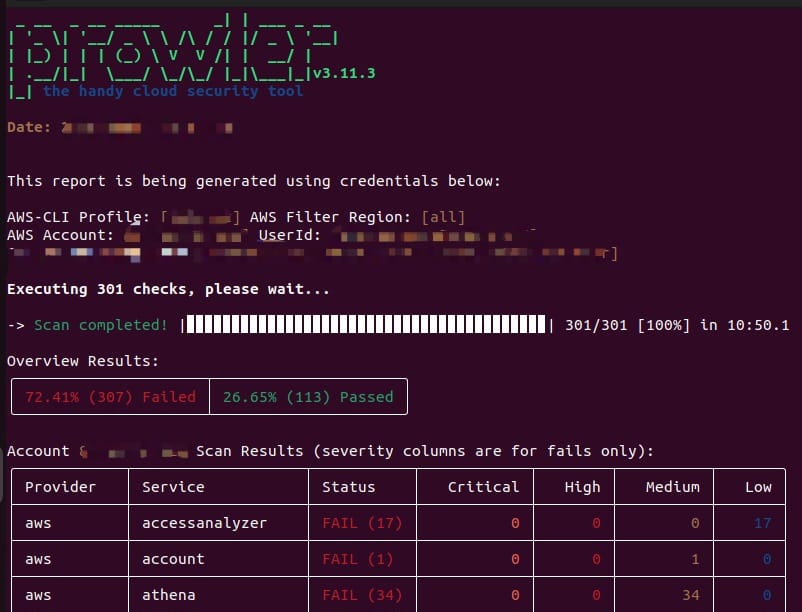
Upon running the Prowler scan, you’ll receive a report in different formats like CSV, JSON, ASFF (Amazon Security Finding Format), and HTML. This detailed report provides insights into your cloud security posture, highlighting potential issues and areas for improvement.
This output acts as a guide for enhancing your security measures, allowing you to address vulnerabilities and ensure compliance with best practices.
But hey, doing all this manually still looks tough and time-consuming, right? Don’t worry; let’s explore how we can automate these tools using a robust Jenkins pipeline. This pipeline won’t just perform the security scan; it will go above and beyond. Imagine it generating a comprehensive scan report and creating an issue on Jira, attaching both security scan reports. Let’s make security not just effective but also efficient. Ready to dive in and discover the power of automation in keeping our AWS and Kubernetes spaces strong and secure?
Automating Security Checks with Jenkins Pipeline
Performing security checks manually can be a daunting task, consuming both time and effort. However, fear not! Let’s delve into the world of automation and discover how we can streamline these processes using a robust Jenkins pipeline.
Key Components and Prerequisites:
Store Secrets in Jenkins Credentials: Ensure your sensitive information, such as Jira API token, Jira username, AWS credentials are securely stored in the Jenkins Secret Manager. This ensures a safe and centralized way to manage credentials.
Required Secrets:
Jira API Token
Jira Username
Jira Project Key
AWS CredentialsJenkins Pipeline Flow:
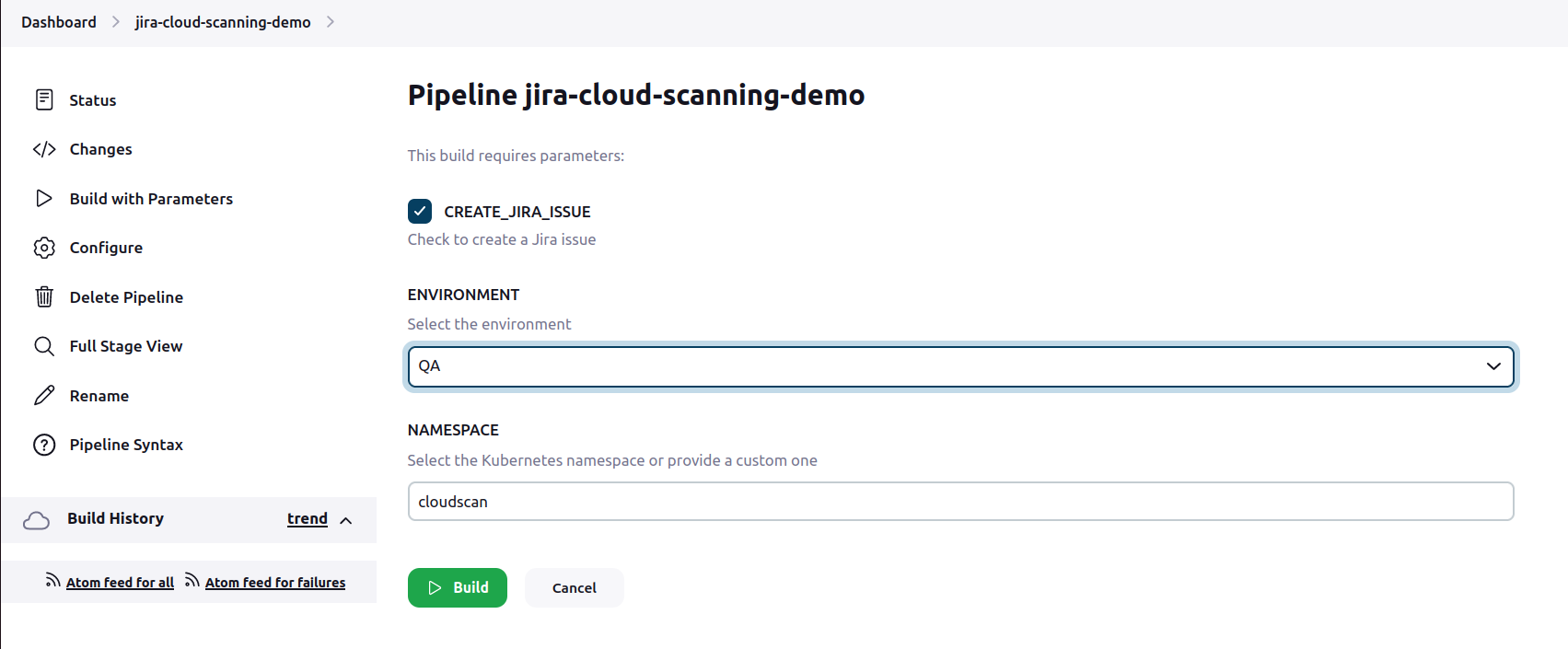
Jenkins pipeline will be designed to offer flexibility and control. Here are the key elements:
Multiple Stages and Parameters: Imagine a setup where you control every note. Our pipeline consists of multiple stages, each playing a crucial role in the security check ballet. Parameters become the key, allowing you to decide whether to scan AWS, Kubernetes, or both.
Parameterized Scans: You can specify parameters in the pipeline to control the scanning process:
Scan AWS: Yes/No
Scan Kubernetes: Yes/No
Create Jira Ticket: Yes/NoSpecify parameters to control the scanning process where you decide if AWS gets its solo, Kubernetes takes the lead, or both can go together. It’s your choice; play it your way.
Dynamic Workflow: The pipeline flow will be dynamic, allowing you to skip certain stages based on your requirements. For instance, if you only want to scan Kubernetes without creating a Jira ticket, you have the flexibility to do so.
GitHub Integration with Poll SCM:
The pipeline will be triggered automatically through GitHub integration, using the “Poll SCM” feature.
Periodic builds will be enabled, ensuring that security scans happen at regular intervals without manual intervention.
Conclusion
In conclusion, safeguarding our digital spaces is crucial, and the combination of tools like Kubebench and Prowler, along with the efficiency of Jenkins automation, makes it achievable. By embracing these security superheroes and automating checks, we not only detect vulnerabilities promptly but also ensure a continuous and robust defense against evolving cyber threats. The power of automation transforms security from a manual task into an integrated, efficient, and effective process, contributing to the resilience of our AWS and Kubernetes environments. Let’s stay secure, stay smart, and let automation pave the way for a safer digital future!
